Debian Installer Jessie Alpha 1 release
 The first alpha of the installation media for Debian 8 (codenamed Jessie) GNU/Linux comes with the lightweight Xfce desktop as standard. The reloading of firmware is not working in this initial version.
The first alpha of the installation media for Debian 8 (codenamed Jessie) GNU/Linux comes with the lightweight Xfce desktop as standard. The reloading of firmware is not working in this initial version.
The Debian installer team has released an initial alpha for Debian 8 (Jessie). The standard images for testing the Jessie installation are supplied with the Xfce desktop as standard. However, it is currently uncertain whether this will be retain for the actual Debian 8 release as the developers want to discuss the standard desktop once more in August. If necessary, the decision taken then will be considered once again, which is possible since the main development phase doesn’t end until 5th November; this “freeze” is typically followed by a stabilisation phase lasting several months before the distribution is finally released.
However, some of the features introduced with the alpha might not be altered any further. Thus there is no alpha version for Itanium (IA-64) processors because the Debian Project will not be supporting this processor architecture in future. In addition, the IBM S390 architecture has been replaced with the S390x architecture.
The AMD64 edition of the first alpha of Jessie takes up three DVDs and uses a kernel which is based on Linux 3.13. Amongst this releases known problems is a bug that missing firmware files cannot be reloaded.
I’m already running Jessie on one of my machines, but did an upgrade on an existing machine, rather than a fresh install, and am finding it very reliable and stable. Read about my experience.
 The government of Italy’s Autonomous Province of South Tyrol wants to save &euro 1 mn. per year by using free software, according to a
The government of Italy’s Autonomous Province of South Tyrol wants to save &euro 1 mn. per year by using free software, according to a  WordPress’ pingback function can be abused to mount a denial of service (DoS) attack on blogs without their owners noticing, Germany’s
WordPress’ pingback function can be abused to mount a denial of service (DoS) attack on blogs without their owners noticing, Germany’s  The Gnome Outreach Program* for Women (OPW) helps women get involved in free and open source software and has just announced the opening of a new round of internship applications. Women can apply for an internship to contribute to an open source project from May to August; and OPW is not just asking for applications from programmers.
The Gnome Outreach Program* for Women (OPW) helps women get involved in free and open source software and has just announced the opening of a new round of internship applications. Women can apply for an internship to contribute to an open source project from May to August; and OPW is not just asking for applications from programmers.

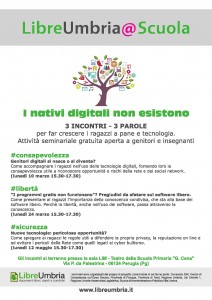 The first of three free seminars organised by LibreUmbria – the organisation promoting free and open source software in Italy’s
The first of three free seminars organised by LibreUmbria – the organisation promoting free and open source software in Italy’s