Why open standards and formats are important
This cartoon strip will tell you the why of the title just as eloquently as I could (possibly more eloquently! Ed.).

Don’t forget that it’s Document Freedom Day on Wednesday 26th March (posts passim).
This cartoon strip will tell you the why of the title just as eloquently as I could (possibly more eloquently! Ed.).

Don’t forget that it’s Document Freedom Day on Wednesday 26th March (posts passim).
 The first alpha of the installation media for Debian 8 (codenamed Jessie) GNU/Linux comes with the lightweight Xfce desktop as standard. The reloading of firmware is not working in this initial version.
The first alpha of the installation media for Debian 8 (codenamed Jessie) GNU/Linux comes with the lightweight Xfce desktop as standard. The reloading of firmware is not working in this initial version.
The Debian installer team has released an initial alpha for Debian 8 (Jessie). The standard images for testing the Jessie installation are supplied with the Xfce desktop as standard. However, it is currently uncertain whether this will be retain for the actual Debian 8 release as the developers want to discuss the standard desktop once more in August. If necessary, the decision taken then will be considered once again, which is possible since the main development phase doesn’t end until 5th November; this “freeze” is typically followed by a stabilisation phase lasting several months before the distribution is finally released.
However, some of the features introduced with the alpha might not be altered any further. Thus there is no alpha version for Itanium (IA-64) processors because the Debian Project will not be supporting this processor architecture in future. In addition, the IBM S390 architecture has been replaced with the S390x architecture.
The AMD64 edition of the first alpha of Jessie takes up three DVDs and uses a kernel which is based on Linux 3.13. Amongst this releases known problems is a bug that missing firmware files cannot be reloaded.
I’m already running Jessie on one of my machines, but did an upgrade on an existing machine, rather than a fresh install, and am finding it very reliable and stable. Read about my experience.
 The government of Italy’s Autonomous Province of South Tyrol wants to save &euro 1 mn. per year by using free software, according to a press release issued last week.
The government of Italy’s Autonomous Province of South Tyrol wants to save &euro 1 mn. per year by using free software, according to a press release issued last week.
Public sector organisations took the first step towards the use of free software nearly one year ago with the change to the LibreOffice productivity suite (news passim). On 11th March 2014 the regional government decided to continue to pursue this route and to resort to the use of open source where possible. “We are expecting savings of one million Euro per year through free software,” declares governor Arno Kompatscher.
“The use of proprietary or free software has in the meantime degenerated into almost a religious war, not only in the public sector, but also in private businesses,” Kompatscher continued, speaking after a regional government meeting.
During the preceding legislature period the region and regional government had already made a decision in principle to opt for the use of free software. In June last year the first major step towards free software was made with the change from MS Office to LibreOffice. The regional government alone migrated 7,000 to the open source office suite.
Governor Kompatscher stressed that it was not a matter of using free software exclusively, but to find the best solution as regards citizens: “We’re standing by using free software. However, it’s not a matter of deciding between free and proprietary software, but between requirements.” Free software, according to Kompatscher, is not always suitable, but: “Citizens must always have access to public sector documents without having to resort to paid-for software as well. That is the key issue”.
The city of Munich is acting as an example for the use of free software in government. “For example, Munich’s city council is using free software; in spite of this ten per cent of its computers are still running proprietary programs. We’re aligning ourselves with this. There will be no either or; the principal objective is friendliness towards citizens,” Kompatscher emphasises.
The governor also refers to the potential savings arising from free software: “A very, very large amount of money is involved. The target is savings of one million euro per year.” Just from its first major step, switching to LibreOffice should save the regional government paying Microsoft some €600,000 in licence fees in the next few years.
 WordPress’ pingback function can be abused to mount a denial of service (DoS) attack on blogs without their owners noticing, Germany’s Heise IT website reports. It is unlikely that the problem will be remedied with an update.
WordPress’ pingback function can be abused to mount a denial of service (DoS) attack on blogs without their owners noticing, Germany’s Heise IT website reports. It is unlikely that the problem will be remedied with an update.
Security company Sucuri reports on an attack on one WordPress installation in which more than 162,000 other WordPress sites were misused as a DDoS platform. In this instance the attacker used the software’s pingback function in order to cripple the target website. With a pingback, one WordPress site can notify another that it has quoted its blog post.
The attack works in such a manner that an attacker searches for a legitimate blog which has pingback activated (currently the default configuration for new WordPress installations) and then simulate a pingback from the victim’s site. The victim’s blog then queries the victim for the post which was quoted in the faked pingback. If the attacker does this with many sites, the flood of traffic is difficult for the target site to black as the queries look completely legitimate and originate from trustworthy sources.
In the attack observed by Sucuri randomly generated URLs were quoted in the fake pingbacks for the victim’s ostensible posts. This results in WordPress’ caching mechanism does not take effect and the web server is so overloaded since the database must attempt to deliver the supposed posts for each request. Of course, in reality the server just serves up 404 error pages, since there are no pages for the random URLs. Nevertheless, if there are many such requests, this is sufficient to cripple the WordPress installation’s database. On Unix and Linux systems such an attack can be launched very simply by using the curl command on the command line.
As the attack is misusing the ordinary working of the pingback function, it cannot be assumed that WordPress developers are going to do something about the problem. Site owners can prevent their blog being miused in this way by deactivating their installation’s pingback functions. Sucuri itself is proposing source code for a WordPress plug-in which should block the attacks, as follows:
add_filter( ‘xmlrpc_methods’, function( $methods ) {
unset( $methods[‘pingback.ping’] );
return $methods;
} );
Use Sicuri’s WordPress DDoS Scanner to check if your site is being used for launching such attacks on other websites.
OmegaT is a free and open source translation memory application written in Java. It’s a tool intended for professional translators.
OmegaT has the following features:
OmegaT is cross-platform: it will run on any system on which the JRE (Java Runtime Environment) has been or can be installed.
Over on YouTube, user weasel75 has produced a short (10 minutes) tutorial on the basics of OmegaT. Hopefully you’ll find it as useful as I did.
 Document Freedom Day is a day for celebrating and raising awareness of open standards and formats; it takes place on the last Wednesday in March each year. On this day people who believe in fair access to communications technology teach, perform and demonstrate.
Document Freedom Day is a day for celebrating and raising awareness of open standards and formats; it takes place on the last Wednesday in March each year. On this day people who believe in fair access to communications technology teach, perform and demonstrate.
Document freedom means documents that are free can be used in any way that the author intends. They can be read, transmitted, edited, and transformed using a variety of tools. Documents that aren’t free – like Microsoft Office’s .docx, .xlsx, .pptx, etc. – are locked to some particular software or company. Their author cannot choose how to use them because they are controlled by technical restrictions. This is akin to having a racehorse and never letting get above a trot.
However, document freedom is about more than spreadsheets, presentations and word processing documents. Document freedom embraces all forms of data, including artwork, sheet and recorded music, emails and statistics. These can all be stored in ways which empower users, but they can also be stored in formats which constrain and manipulate us at enormous cost.
Open standards are formats which everybody can use free of charge and restriction. They come with compatibility “built-in” – the way they work is shared publicly and any organisation can use them in their products and services without asking for permission. Open Standards are the foundation of cooperation and modern society. Today we celebrate the 25th anniversary of the world wide web – a vital resource that relies on open standards to work. Read more on open standards.
You can get involved in Document Freedom Day by organising local activities, distributing fliers, adding a banner on your blog, donating money, and much more. See the Document Freedom Day site for more ideas and information.
My LinkedIn timeline has just turned up a link to the following video.
Hat tip: Paolo Vecchi of Omnis Systems.
 The Gnome Outreach Program* for Women (OPW) helps women get involved in free and open source software and has just announced the opening of a new round of internship applications. Women can apply for an internship to contribute to an open source project from May to August; and OPW is not just asking for applications from programmers.
The Gnome Outreach Program* for Women (OPW) helps women get involved in free and open source software and has just announced the opening of a new round of internship applications. Women can apply for an internship to contribute to an open source project from May to August; and OPW is not just asking for applications from programmers.
Successful applicants can obtain a Gnome Foundation internship from 19th May until 18th August 2014 under the aegis of the OPW. The outreach programme is intended to increase the proportion of women in open source projects and twice a year promotes the contribution of women to projects such as Gnome, Wikimedia and OpenStack. The deadline for applications for the next round is 19th May 2014.
As previously stated, the programme is not restricted to women with programming skills; those with design, documentation or marketing skills can also apply. All participants will be supported by a mentor in the participating organisations. Details on how to apply are on the Gnome Foundation’s dedicated OPW site.
* = It’s an American institution, hence the US spelling.
 France’s Le Monde reports that a very powerful computer virus has infected computers in Ukraine, where 22 instances of infection has been recorded since 2013, the year that country’s political crisis started, according to a report from BAE Systems.
France’s Le Monde reports that a very powerful computer virus has infected computers in Ukraine, where 22 instances of infection has been recorded since 2013, the year that country’s political crisis started, according to a report from BAE Systems.
This virus, baptised Snake, but also known as Ouroboros after the serpent in Greek mythology, is “one of the most sophisticated and persistent threats that we track,” states BAE Systems Applied Intelligence, in a report published on Friday, 7th March.
Although it appeared as early as 2006, Snake appears to have been deployed more aggressively since 2013, according to the same source: of the 56 instances identified since 2010 throughout the world, 44 have been recorded since last year. Ukraine is the main target with 22 instances since 2013, of which 14 alone have been confirmed since the start of 2014 when that country’s political crisis accelerated with the fall of its pro-Russian president at the end of February.
Lithuania, Britain and Georgia are amongst the other countries where Snake has also shown up.
Snake’s operators act on weekdays and operate mainly from a time zone corresponding to Moscow, BAE Systems states. “Our report shows that a technically sophisticated and well-organised group has been developing and using these tools for the last eight years,” said David Garfield, the managing director of cyber security at BAE Systems Applied Intelligence.
“There is some evidence that links these tools to previous breaches connected to Russian threat actors but it is not possible to say exactly who is behind this campaign.”
Snake’s controllers can access all of the computer systems they have infiltrated, in addition to which the virus’ capacity to hibernate by remaining completely inactive for many days makes its detection complex.
According to Saturday’s Financial Times (paywall), the virus has in particular infiltrated the Kiev government’s computer systems and those of major Ukrainian organisations.
According to IT security vendors Kaspersky Lab, the Tor anonymity network is under threat of being swamped by criminals abusing the anonymity it provides for hiding zombie networks, malicious command and control servers and ‘darknets’, Le Monde Informatique reports.
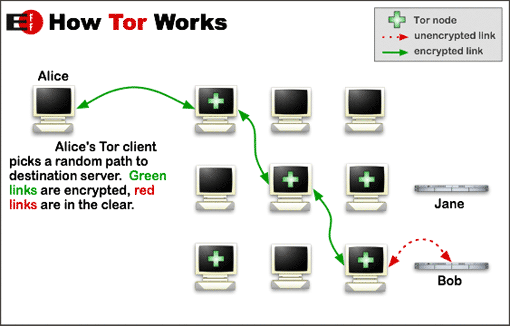
Tor – otherwise known as The Onion Router – has always had its dark side, but last year the network’s use by criminals seems to have grown appreciably. According to researcher Sergey Lozhkin, “Kaspersky Lab had uncovered evidence of 900 services using Tor, equivalent to 5,500 nodes (server relays) and 1,000 exit nodes (servers from which traffic emerges) in total.”
“It all started from the notorious Silk Road market and evolved into dozens of specialist markets: drugs, arms and, of course, malware.
“Carding shops are firmly established in the Darknet. Stolen personal info is for sale with a wide variety of search attributes like country, bank, etc. Offers for customers of this kind are not limited to credit cards. Dumps, skimmers and carding equipment are for sale too”, he added.
“In addition, command and control (C&C) servers hosted by Tor are more difficult to flush out, blacklist or eliminate,” Lozhkin continued. “Although creating a Tor communication module within a malware sample means extra work for the malware developers. We expect there will be a rise in new Tor-based malware, as well as Tor support for existing malware.”
Experts from Kaspersky Lab have so far found Zeus with Tor capabilities and then detected ChewBacca and finally analysed the first Tor Trojan for Android.